Secure Mobile App Development: Protect Users
15 min
read
Security can't be an afterthought in mobile app development. Learn how to build user data protection into your app from day one.

A single security breach can destroy years of customer trust overnight. Mobile apps handle passwords, payment details, health records, and personal data that attackers actively target every day.
Secure mobile app development is not a feature you add later. It must be part of every decision from architecture to deployment. This guide covers the practices, tools, and strategies behind building mobile apps that protect users from real threats.
Key Takeaways
- Security starts at architecture because retrofitting protections into a poorly designed app is expensive, incomplete, and unreliable.
- Data encryption is the minimum baseline with both data-in-transit and data-at-rest requiring strong encryption standards.
- Authentication must go beyond passwords through biometrics, multi-factor authentication, and token-based session management.
- API security prevents backend attacks since most mobile app breaches happen through poorly secured server communication endpoints.
- Regular security testing catches vulnerabilities before attackers find them through penetration testing, code scanning, and threat modeling.
- Compliance requirements vary by industry and failing to meet HIPAA, PCI DSS, or GDPR standards creates legal and financial liability.
Why Is Security Critical in Mobile App Development?
Security is critical because mobile apps collect, store, and transmit sensitive personal data. A breach exposes users to identity theft, financial loss, and privacy violations while destroying business reputation.
Mobile devices are the most targeted attack surface in technology today. Every mobile app you build is a potential entry point for attackers seeking access to user data and backend systems.
- Personal data theft affects millions when mobile apps with weak security expose user credentials, payment details, and private information.
- Financial liability follows breaches through regulatory fines, lawsuits, compensation costs, and lost revenue from damaged brand reputation.
- Regulatory penalties are severe with GDPR fines reaching 4 percent of global revenue and HIPAA violations costing millions per incident.
- App store rejection blocks launches because both Apple and Google increasingly enforce security standards during the review process.
- User trust is impossible to rebuild once customers learn their data was compromised through your mobile app's security failures.
- Competitive advantage erodes permanently when security incidents drive customers to competitors who handle their data more responsibly.
Secure mobile app development is not optional for any organization handling user data. Understanding security liability and IP risk helps you take the right precautions before problems occur.
What Are the Most Common Mobile App Security Vulnerabilities?
The most common vulnerabilities include insecure data storage, weak authentication, unprotected API endpoints, insufficient encryption, and improper session handling. Most breaches exploit well-known weaknesses, not novel attacks.
Mobile app security failures follow predictable patterns. The Open Web Application Security Project (OWASP) documents the most common mobile vulnerabilities, and most successful attacks exploit these known weaknesses.
- Insecure data storage exposes information when apps save sensitive data in plain text on the device without encryption or protection.
- Weak authentication allows unauthorized access when apps rely on simple passwords without rate limiting, lockout, or multi-factor verification.
- Unprotected API endpoints invite attacks because backend services without proper authentication and input validation are easily exploited remotely.
- Insufficient transport encryption lets attackers intercept data in transit through man-in-the-middle attacks on unprotected network connections.
- Improper session management allows session hijacking when tokens do not expire, rotate, or validate correctly on each request.
- Code injection vulnerabilities let attackers execute malicious code when apps fail to sanitize user input before processing it.
Knowing these vulnerabilities is the first step toward preventing them. Your mobile app testing and QA process must specifically test for each of these common attack vectors before every release.
How Do You Secure Data Storage in Mobile Apps?
Secure data storage requires encrypting all sensitive data on the device, using platform-provided secure storage APIs, avoiding plain-text logging, and implementing remote wipe capabilities for lost devices.
Data stored on mobile devices is vulnerable to extraction through physical access, malware, and backup exploitation. Secure mobile app development assumes the device itself could be compromised at any time.
- Platform keychain and keystore APIs provide hardware-backed encryption for storing credentials, tokens, and encryption keys securely.
- Database encryption protects local data by encrypting SQLite or Realm databases so extracted files are unreadable without the encryption key.
- Avoid logging sensitive information because debug logs containing tokens, passwords, or personal data persist on devices and in crash reports.
- Disable backup for sensitive data by flagging critical files as excluded from iCloud and Google backups that users may not secure properly.
- Remote wipe capabilities protect lost devices by letting administrators erase app data when a device is reported lost or stolen.
Secure data storage is foundational to secure mobile app development. Every piece of sensitive data on the device should be encrypted, and you should minimize what you store locally in the first place.
What Authentication Methods Should Secure Mobile Apps Use?
Secure mobile apps should use multi-factor authentication, biometric verification, OAuth 2.0 with PKCE, token-based session management, and adaptive authentication that increases security for sensitive actions.
Authentication is the front door of your mobile app. Weak authentication is the single most exploited vulnerability in mobile applications, and strengthening it blocks the majority of unauthorized access attempts.
- Multi-factor authentication adds layers by requiring something the user knows, has, or is before granting access to sensitive features.
- Biometric authentication uses fingerprint or face recognition to verify identity quickly while providing stronger security than passwords alone.
- OAuth 2.0 with PKCE secures third-party login by implementing the Proof Key for Code Exchange flow designed specifically for mobile apps.
- Token rotation prevents session hijacking by issuing short-lived access tokens and refresh tokens that change with each use.
- Adaptive authentication adjusts dynamically by requiring additional verification for high-risk actions like changing passwords or making large payments.
Strong authentication protects your users without creating excessive friction. The mobile app development process should include authentication architecture review early in the design phase.
How Do You Secure Mobile App API Communication?
Secure API communication by enforcing HTTPS everywhere, implementing certificate pinning, validating all inputs server-side, using API keys with rate limiting, and authenticating every request with bearer tokens.
Most mobile app attacks target the APIs that connect the app to its backend servers. The communication layer between your mobile app and your servers is the most attacked surface in mobile architecture.
- HTTPS is mandatory for all traffic because any unencrypted communication can be intercepted and read by attackers on the same network.
- Certificate pinning prevents interception by hardcoding your server's certificate in the app so fake certificates are automatically rejected.
- Server-side input validation blocks injection because client-side validation alone can be bypassed by attackers who manipulate API requests directly.
- Rate limiting prevents abuse by restricting how many requests a single user or IP address can make within a given time window.
- Bearer tokens authenticate every request ensuring the server verifies the identity and permissions of the requester before processing any action.
- API versioning enables security updates by letting you deprecate vulnerable endpoints while maintaining backward compatibility for existing app versions.
API security requires collaboration between mobile and backend teams. Secure mobile app development treats the API layer as the primary attack surface and designs defenses accordingly from the beginning.
How Do You Build a Security-First Development Culture?
Build a security-first culture by training developers on secure coding practices, integrating security checks into CI/CD pipelines, conducting regular code reviews focused on security, and rewarding teams that identify vulnerabilities early.
Secure mobile app development is not just about tools and processes. It requires a team culture where every developer considers security implications in every line of code they write.
- Security training for all developers ensures the team understands common vulnerabilities and knows how to write code that prevents them.
- Automated security scanning in CI/CD pipelines catches vulnerable dependencies and insecure patterns before code reaches production environments.
- Security-focused code reviews add a review step where a team member specifically evaluates changes for security weaknesses and data exposure risks.
- Threat modeling during feature planning identifies potential attack vectors before development begins so defenses are designed into the feature.
- Bug bounty programs incentivize external testing by paying security researchers who discover and responsibly disclose vulnerabilities in your app.
- Post-incident reviews prevent recurrence by analyzing every security event to identify root causes and implement systemic improvements.
A security-first culture costs less than a single data breach. Teams that treat security as a shared responsibility produce more secure apps than those who delegate security to a single specialist.
Building security awareness into your team culture is an investment that pays dividends across every project and every release for years to come.
What Role Does Security Testing Play in Mobile App Development?
Security testing identifies vulnerabilities before attackers exploit them. It includes static code analysis, dynamic testing, penetration testing, and dependency scanning throughout the development lifecycle.
Testing is where secure mobile app development proves itself. Without systematic security testing, you are relying on assumptions that your code is secure rather than evidence that it actually is.
- Static code analysis scans source code for security vulnerabilities, hardcoded secrets, and insecure patterns before the code ever runs.
- Dynamic application testing finds runtime issues by testing the running app for vulnerabilities that only appear during actual execution.
- Penetration testing simulates real attacks by hiring security professionals to attempt breaking into your app using the same techniques attackers use.
- Dependency scanning catches vulnerable libraries by monitoring third-party packages for known security vulnerabilities that need patching.
- Threat modeling identifies attack surfaces by mapping every data flow, entry point, and trust boundary in your app's architecture.
Security testing is not a one-time activity. Your post-launch maintenance plan must include regular security assessments because new vulnerabilities emerge constantly as attackers develop new techniques.
How Do Compliance Requirements Shape Secure Mobile App Development?
Compliance requirements shape development by mandating specific encryption standards, data handling procedures, audit capabilities, breach notification processes, and privacy controls based on your industry and user geography.
Different industries and regions impose different security requirements on mobile apps. Meeting compliance is not optional, and violations carry penalties that can threaten the viability of your entire business.
Build compliance into your app from the start rather than retrofitting it before an audit. Compliance-driven design decisions are cheaper to implement during development than they are to add after launch.
Engage a compliance consultant early in the project if your app handles healthcare, financial, or children's data, because the cost of expert guidance upfront is a fraction of the cost of failing an audit or facing regulatory action after deployment.
How Do You Handle Secure Data Transmission Between Mobile and Backend?
Handle secure data transmission by implementing TLS 1.3 for all connections, using certificate pinning to prevent interception, encrypting sensitive payloads before transmission, and validating data integrity on both ends.
Data moves constantly between your mobile app and backend servers. Every API call, authentication request, and data sync creates an opportunity for attackers to intercept, modify, or steal information in transit.
- TLS 1.3 provides the strongest transport encryption by using modern cipher suites that protect data between the app and server.
- Payload encryption adds a second layer by encrypting sensitive data within the request body so intercepted traffic remains unreadable.
- Certificate transparency monitoring detects rogue certificates by alerting your team when unauthorized certificates are issued for your domains.
- Request signing prevents tampering by adding cryptographic signatures that the server verifies before processing any incoming request.
- Network security configuration restricts connections by defining which domains the app can communicate with and blocking all others.
Secure data transmission is a baseline requirement that every mobile app must implement correctly. Failures at this layer expose every piece of data your users share with your app to potential interception.
Audit your data transmission security with every major release, because new endpoints, API changes, and third-party integrations can introduce vulnerabilities that did not exist in previous versions.
How Do You Maintain Security After Launching a Mobile App?
Maintain security through regular dependency updates, security patch releases, ongoing penetration testing, real-time monitoring, incident response planning, and compliance audits on a defined schedule.
Launching a secure mobile app is the beginning, not the end, of your security responsibility. Threats evolve continuously, and risk management must be an ongoing operational commitment.
- Dependency updates patch known vulnerabilities because third-party libraries you use today may have critical security flaws discovered tomorrow.
- Security monitoring detects attacks in progress through real-time alerting on suspicious API activity, failed login attempts, and data anomalies.
- Incident response plans prepare your team with documented procedures for containing breaches, notifying users, and recovering from security events.
- Regular penetration tests reveal new weaknesses because app updates, new features, and infrastructure changes can introduce vulnerabilities unintentionally.
- Compliance audits confirm ongoing adherence to industry regulations that change over time and require documented proof of security practices.
- User education reduces social engineering risk by teaching users to recognize phishing attempts and protect their account credentials.
Security maintenance should be budgeted as an ongoing cost, not treated as an afterthought. The cost of maintaining security is always lower than the cost of recovering from a breach.
Ready to Build a Secure Mobile App?
Secure mobile app development protects your users, your reputation, and your business from threats that grow more sophisticated every year. Security cannot be bolted on after launch. It must be designed in from day one.
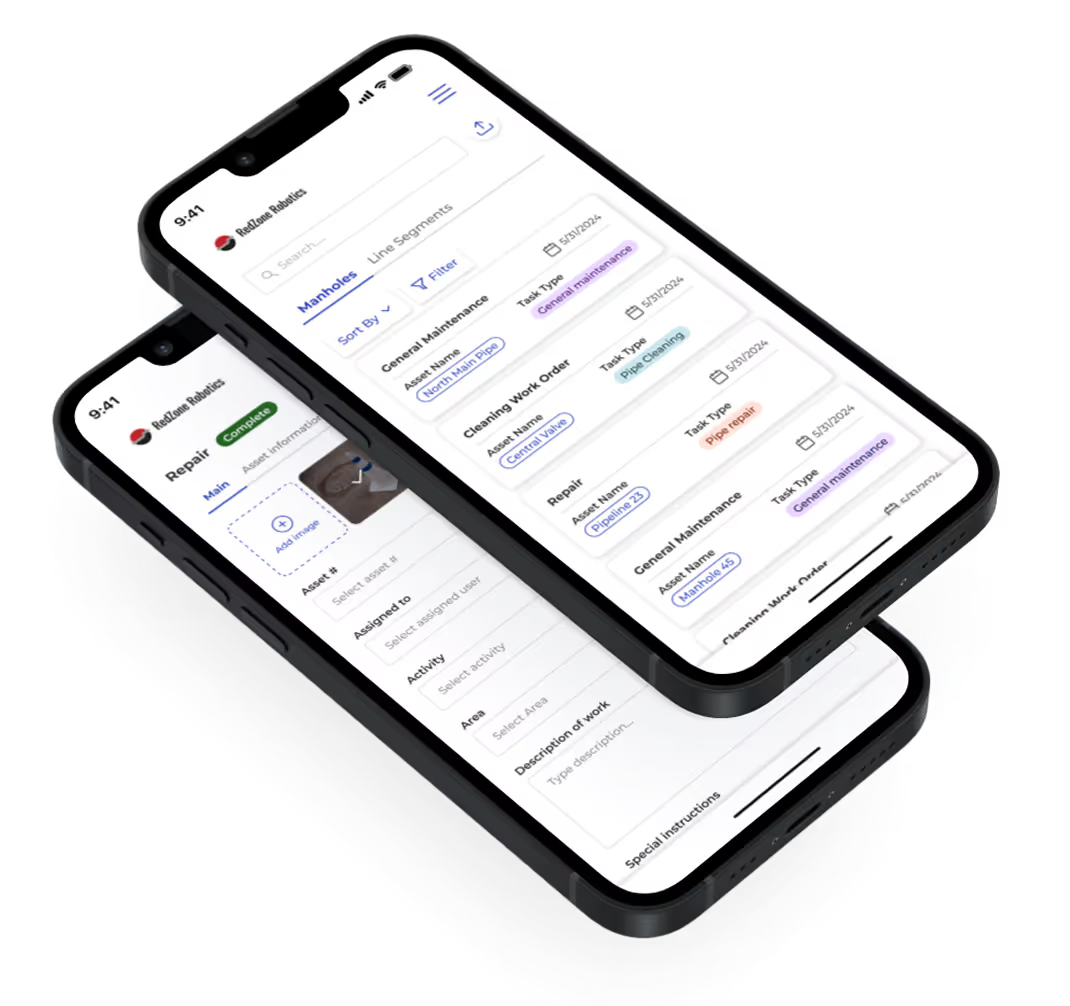
LowCode Agency is a strategic product team, not a dev shop. We build secure mobile apps with security integrated into every phase from architecture design through post-launch monitoring and maintenance.
- Discovery includes threat modeling so security architecture is designed around your specific data, users, and regulatory requirements.
- Design implements secure patterns with authentication flows, data handling, and API communication designed to resist known attack vectors.
- Build follows secure coding standards with encrypted storage, certificate pinning, input validation, and security testing throughout development.
- Scalability includes security at scale so growing user bases and increased traffic do not create new vulnerabilities or performance-based attack surfaces.
- Delivery includes security testing with penetration testing, code scanning, and vulnerability assessment before any app reaches production.
- Partnership provides ongoing security through monitoring, patch management, compliance audits, and incident response support after launch.
Over 350 projects delivered for clients including Medtronic, American Express, Coca-Cola, Zapier, and Sotheby's. We build across FlutterFlow, Bubble, Glide, Webflow, Make, n8n, and Zapier.
If you are serious about building a secure mobile app, let's build it properly.
Our team at LowCode Agency will help you design, build, and maintain an app your users can trust with their data.
Last updated on
March 24, 2026
.

FAQs
What are the most important security practices in mobile app development?
How do I secure user authentication in my mobile app?
What is certificate pinning and should my mobile app use it?
How do I protect sensitive data stored on a mobile app user's device?
What compliance standards apply to mobile app security?
How often should I conduct a security audit for my mobile app?