Mobile App Security, Liability & IP Risk
14 min
read
Is your mobile app secure and legally protected? Learn how to manage security risks, liability exposure, and intellectual property rights.

A single data breach costs the average company $4.45 million. A single intellectual property dispute can freeze your product indefinitely. Mobile app security, liability, and IP risk are not technical afterthoughts. They are existential threats that can destroy your business faster than a bad product ever could.
Most founders treat mobile app security as a development concern and IP as a legal one. In reality, mobile app security, liability, and IP risk are intertwined business risks that require integrated planning across your technical, legal, and product teams. This guide covers how to address all three.
Key Takeaways
- Security vulnerabilities expose your company: to regulatory fines, lawsuits, and reputational damage that can exceed the cost of the app itself.
- Liability falls on the app owner: not the development agency, unless your contract explicitly transfers specific security obligations.
- IP risk includes: code ownership disputes, open-source license violations, and trade secret exposure through third-party contractors.
- Security and IP risk must be addressed: in contracts, architecture, development practices, and post-launch monitoring simultaneously.
- Regulatory compliance requirements: like GDPR, CCPA, and HIPAA create specific mobile app security obligations that carry statutory penalties for violations.
- Upfront investment of $10K to $30K: in mobile app security testing and IP protection prevents losses that routinely reach six or seven figures when breaches or disputes occur.
What Are the Biggest Mobile App Security Risks?
The biggest mobile app security risks are insecure data storage, weak authentication, unencrypted network communication, vulnerable third-party libraries, and insufficient server-side validation.
Mobile app security threats evolve constantly, but the most damaging breaches consistently exploit the same fundamental weaknesses. Understanding these risks is the first step in building a mobile app that protects your users and your business.
- Insecure data storage exposes sensitive information when mobile app security practices fail to encrypt user data stored on the device or in local databases.
- Weak authentication enables unauthorized access because mobile app security depends on proper implementation of password hashing, token management, and session controls.
- Unencrypted network traffic allows interception when mobile app security neglects TLS/SSL for all API communications, exposing data in transit to man-in-the-middle attacks.
- Third-party library vulnerabilities create backdoors since mobile app security is only as strong as the weakest dependency in your technology stack.
- Insufficient server-side validation trusts client input which is a mobile app security failure that enables SQL injection, cross-site scripting, and data manipulation attacks.
- Improper session management allows session hijacking when mobile app security does not implement proper token expiration, refresh rotation, and device binding.
Address these mobile app security risks during architecture and development, not after launch. Retrofitting security into a mobile app costs 3x to 10x more than building it in from the start. Security is an architecture decision, not a feature, and it must be embedded in the foundation of your mobile app from the first sprint.
Who Is Liable When a Mobile App Has a Security Breach?
The mobile app owner bears primary liability for security breaches. Your development agency may share liability only if your contract includes specific security obligations, warranties, and indemnification clauses.
Liability for mobile app security breaches is a legal question that most founders have not considered until the breach happens. The default legal position places responsibility on the entity that collects, stores, and processes user data, which is you.
- Data controller liability applies to app owners because mobile app security regulations hold the entity collecting data responsible, not the entity that wrote the code.
- Regulatory fines target the business with GDPR penalties up to 4% of annual revenue and CCPA fines up to $7,500 per intentional violation for mobile app security failures.
- Class action lawsuits name the app owner since users whose data was exposed in a mobile app security breach sue the company whose app they trusted with their information.
- Agency liability requires contractual transfer because unless your contract explicitly assigns mobile app security responsibilities, the agency has no default legal obligation.
- Insurance covers some mobile app security liability through cyber liability policies that typically cost $1,000 to $7,500 annually depending on your data volume and risk profile.
Consult a technology attorney about mobile app security liability before you launch. Understanding your exposure shapes the security investments you need to make and the contract terms you need to negotiate.
How Do You Protect Your Mobile App's Intellectual Property?
Protect mobile app IP through explicit code ownership contracts, patent filings for novel functionality, trademark registration for your brand, trade secret protections for proprietary algorithms, and NDA agreements with all contributors.
IP risk in mobile app development takes multiple forms, and each requires a different protection strategy. A comprehensive approach to mobile app security, liability, and IP risk addresses all of these vectors before they create disputes.
- Code ownership contracts must be explicit because mobile app IP defaults to the creator unless a written assignment transfers rights to you as the paying client.
- Patent filings protect novel functionality when your mobile app includes unique algorithms, processes, or technical innovations that competitors could replicate.
- Trademark registration covers your brand including your mobile app name, logo, and distinctive UI elements that identify your product in the marketplace.
- Trade secret protections guard proprietary data by requiring NDAs and access controls that prevent your mobile app's competitive advantages from being shared.
- Open-source license compliance prevents IP contamination since mobile app development frequently uses open-source libraries with licenses that impose obligations on your commercial use.
IP protection for mobile apps is not a one-time event. It requires ongoing vigilance as your development team changes, your technology evolves, and your competitive landscape shifts.
What Regulatory Compliance Requirements Affect Mobile App Security?
GDPR, CCPA, HIPAA, PCI-DSS, and SOC 2 are the primary regulatory frameworks that impose specific mobile app security requirements depending on your users' location, the data you collect, and the industry you operate in.
Regulatory compliance is not optional for mobile app security. Violating these frameworks carries statutory penalties that are enforced regardless of whether a breach actually occurred. Mobile app security must be designed around compliance from the start.
- Identify applicable regulations early because mobile app security architecture must accommodate compliance requirements that are expensive to retrofit after development.
- Privacy by design is legally required under GDPR, meaning mobile app security must consider data protection from the initial architecture decisions forward.
- Regular compliance audits verify ongoing adherence since mobile app security regulations require continuous compliance, not just compliance at launch.
- Documentation of security practices is mandatory because regulatory investigations examine your mobile app security processes and policies, not just your technology.
Map your regulatory obligations before development begins. Your mobile app security architecture must be designed to comply with every applicable regulation from the first line of code.
How Should Your Contract Address Mobile App Security and IP Risk?
Your contract should include security standards requirements, breach notification obligations, indemnification clauses, IP assignment provisions, and warranty periods for security-related defects.
The contract between you and your development partner is where mobile app security, liability, and IP risk protections become enforceable. Generic contracts leave gaps that become expensive when incidents occur.
- Security standards clauses define minimum requirements including encryption standards, authentication methods, and coding practices that the mobile app must meet.
- Breach notification obligations set response timelines requiring your development partner to notify you within 24 to 48 hours of discovering any mobile app security vulnerability.
- Indemnification clauses shift specific liability so your development partner bears responsibility for mobile app security failures attributable to their negligence.
- IP assignment provisions transfer all rights including source code, designs, algorithms, and documentation created during mobile app development to you as the owner.
- Security warranty periods of 90 to 180 days require the development partner to fix mobile app security vulnerabilities discovered after launch at no additional cost.
- Audit rights allow independent security testing giving you the right to have third parties assess mobile app security at any point during and after development.
Invest in legal review of these specific clauses. The $3K to $8K cost of specialized contract review is trivial compared to the mobile app security liability exposure from inadequate protections.
How Much Does Mobile App Security Cost?
Comprehensive mobile app security costs $10K to $30K during development for secure architecture and coding practices, plus $5K to $15K annually for penetration testing, monitoring, and compliance maintenance.
Mobile app security is an investment, not an expense. The cost of prevention is a fraction of the cost of response. Companies that invest in mobile app security upfront spend 60% to 80% less on security-related incidents over the product lifecycle.
- Secure architecture design adds $3K to $8K to the initial mobile app development cost for threat modeling, security architecture review, and compliance planning.
- Secure coding practices add 10% to 15% to development time because mobile app security requires code review, input validation, and encryption implementation throughout the build.
- Penetration testing costs $5K to $15K per assessment and should be conducted before launch and annually to identify mobile app security vulnerabilities that internal testing misses.
- Security monitoring tools cost $200 to $2,000 monthly for runtime application self-protection, vulnerability scanning, and anomaly detection in production mobile app environments.
- Compliance certification costs $10K to $50K depending on the framework, with SOC 2 and HIPAA audits at the higher end of the range for mobile app security compliance.
- Incident response planning costs $2K to $5K for creating the mobile app security playbook that guides your team through breach detection, containment, and notification.
Budget for mobile app security as a line item alongside cloud infrastructure and autoscaling costs, not as an optional add-on. The investment pays for itself by preventing the incidents that cost orders of magnitude more.
What Should Your Mobile App Security Testing Strategy Include?
Your mobile app security testing strategy should include static code analysis, dynamic testing, penetration testing, dependency scanning, and compliance validation conducted at regular intervals throughout development and after launch.
Mobile app security testing is not a single event before launch. It is a continuous practice that must evolve as your application changes, new threats emerge, and regulatory requirements update.
- Static code analysis runs on every commit scanning mobile app source code for known vulnerability patterns, insecure coding practices, and hardcoded secrets automatically.
- Dynamic testing simulates attacks against running code to find mobile app security vulnerabilities that only appear when the application is executing in a real environment.
- Penetration testing by independent experts provides an adversarial assessment of mobile app security that internal teams cannot replicate due to familiarity bias.
- Dependency scanning checks third-party libraries for known vulnerabilities in the mobile app's supply chain, which is one of the fastest-growing attack vectors in mobile app security.
- Compliance validation confirms regulatory adherence by testing mobile app security controls against the specific requirements of GDPR, HIPAA, PCI-DSS, or other applicable frameworks.
- API security testing covers all endpoints since mobile app security depends heavily on the server-side APIs that handle authentication, data access, and business logic.
Integrate security testing into your CI/CD pipeline so mobile app security is verified with every release, not just during scheduled assessments. Automated testing catches regressions before they reach production.
How Do You Build a Mobile App Security Incident Response Plan?
Build an incident response plan by defining detection procedures, escalation paths, containment steps, notification obligations, and post-incident review processes before any mobile app security breach occurs.
A mobile app security incident response plan is the document your team follows when a breach is detected. Without one, every decision is made under pressure, and pressure produces mistakes that amplify the damage.
- Detection procedures define how you identify breaches including monitoring alerts, user reports, and automated scanning that trigger the mobile app security incident response process.
- Escalation paths name specific people with clear roles including incident commander, technical lead, legal counsel, and communications lead for mobile app security events.
- Containment steps describe immediate technical actions like revoking compromised tokens, isolating affected systems, and preserving evidence of the mobile app security breach.
- Notification timelines comply with regulations since GDPR requires breach notification within 72 hours and other frameworks have their own mobile app security disclosure requirements.
- Post-incident review identifies root causes and produces specific improvements to mobile app security practices that prevent the same vulnerability from being exploited again.
- Annual tabletop exercises test the plan by simulating mobile app security incidents so your team practices the response before a real breach occurs.
Create the incident response plan during development, not after launch. Mobile app security incidents happen without warning, and the only effective response is one that was planned, documented, and practiced in advance.
Conclusion
Mobile app security, liability, and IP risk are interconnected threats that require coordinated protection across your technical architecture, legal agreements, development practices, and ongoing operations. A security breach exposes you to financial, legal, and reputational damage. An IP dispute can freeze your product entirely.
Both are preventable with upfront investment in the right protections. Budget for security, negotiate strong contracts, test continuously, and treat mobile app security as a business priority, not a technical checkbox.
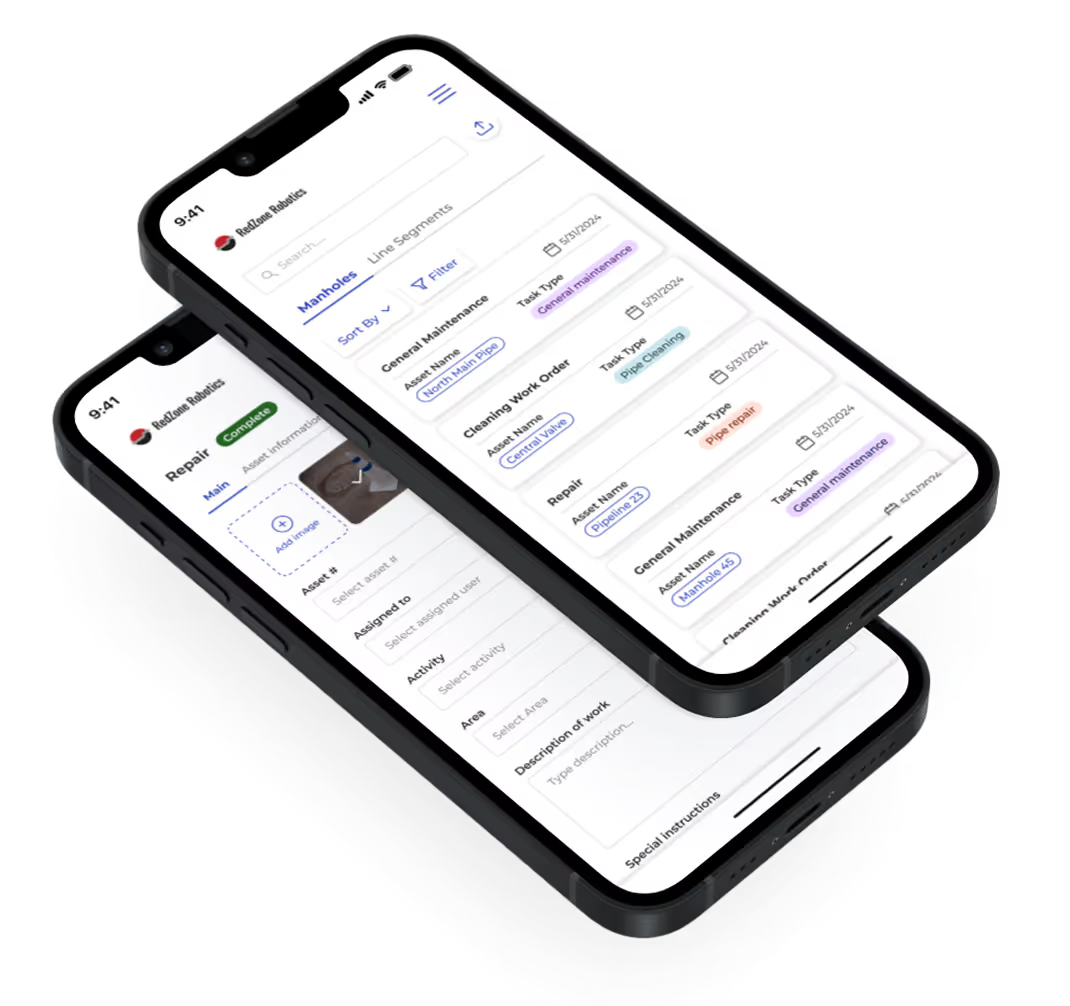
Build Your Mobile App with LowCode Agency
LowCode Agency is a strategic product team, not a dev shop. We build mobile app security, liability, and IP protections into every engagement because we understand that a secure, properly owned product is the foundation of a successful business.
- Security-first development practices including encrypted data handling, secure authentication, input validation, and OWASP compliance on every mobile app build.
- Clear IP ownership and code transfer with explicit assignment clauses, client-owned repositories, and progressive ownership tied to milestone payments.
- Compliance-aware architecture designed to meet GDPR, CCPA, HIPAA, and PCI-DSS requirements based on your specific regulatory obligations.
- 350+ projects delivered for clients including Medtronic, American Express, Coca-Cola, Zapier, and Sotheby's with security and IP protections built into every engagement.
- Post-launch security support including vulnerability monitoring, penetration testing coordination, and security patch management for your mobile app.
- Transparent contracts with security warranties that define our obligations, your protections, and the accountability standards for mobile app security throughout the engagement.
Get in touch with our team to discuss your mobile app project with a development partner that takes security, liability, and IP risk as seriously as you do.
Last updated on
March 24, 2026
.

FAQs
What are the biggest security risks in mobile app development?
How do I protect user data in my mobile app?
Who is liable if my mobile app is hacked and user data is exposed?
Who owns the intellectual property in a mobile app project?
What privacy regulations apply to mobile apps?
How do I protect my mobile app idea from being copied by the agency I hire?